The Price Cybercriminals Charge for Stolen Data
For the price of a Starbuck’s Caramel Frappuccino Grande and a cheese Danish, about $8, a cybercriminal can obtain all the information needed to max out a person’s stolen credit card and possibly steal their identity.
This is just one example dredged from the Dark Web by the elite Trustwave SpiderLabs team while it was conducting research for an exhaustive study into what cybercriminals charge for stolen records.
The team found repositories of financial and identity records along with VPN and remote desktop access credentials in various Darknet markets and uncovered a complicated pricing structure that sees threat actors pricing their information in the same manner as any seller on a legitimate retail site. Prices vary depending upon the country from which the information was stolen and the quality and depth of the content associated with the credential.
So, why are these records sold instead of used by the thieves? The answer is simple expediency. Criminals opt to sell credit card and driver’s license information wholesale instead to quickly cash out and to avoid the time and trouble required to use the assets.
Generally, threat actors’ activity is divided into business fields, someone is digging, attacking, and others are selling data or extracting user information and using it to obtain money. If the hacker or group does not know how to use the stolen information – they sell it. SpiderLabs found that in most cases, what is being sold on a forum was previously sold or used by a hacker. So, a buyer may not get first-hand hacked data.
And these threat actors do cash out. For example, the FBI’s 2021 Internet Crime Report stated credit card fraud in the U.S. resulted in $172,998,385 in losses, and this only takes into account reported incidents.
What’s For Sale on the Dark Web?
The better question is – what is not for sale on the Dark Web, but let’s focus on financial, identification and access data.
Here is a quick list of the items SpiderLabs found:
- Credit cards
- Bank account information
- Access to organizations through their VPNs and other means
- Social Security numbers
- Passports
- Driver’s licenses
- And the ability to create the supporting documentation to prove these credentials belong to the purchaser.
| Item name | Price range in USA | Price range in EU | Price range Asia | Comments |
| Cloned Cards and Fullz | $50 - $1500 per item | same | same | The price depends on how much credit would be provided for the card. |
| Common Credit Card, with Fullz | $8 - $70 | $25 - $70 | $50 - $90 | This is a price for one card, in most cases it comes with full info |
| CC Track 1&2 | $30 - $140 | $50 - $100 | $50 - $120 | Price depends on CC class: Classic Gold Platinum Business Signature Purchase Corporate World |
| Bank account access | $100 - $3000 | $100 - $3000 | $100 - $3000 | Price depends on account bank checking. And probable credit abilities. |
| Stealer Logs selling | $1 - $100 | The logs from stealer could contain trash but could have your bank session. Depends on how many times info was extracted from logs, target. | ||
| FTP/RDP/SSH/VNC/VPN/ Organization access | $50 - $2000 | $50 - $2000 | $50 - $2000 | The price could be much higher, depends on company revenue, targeted interest. |
| Social Security Numbers | $0.20 - $5 | The logs from stealer could contain trash but could have your bank session. Depends on how many times info was extracted from logs, target. | ||
| ID, Passport, Driver’s license | $1 - $50 | $1 - $50 | $1 - $50 | The quality or uniqueness of the document has high role here |
| Selfie with your documents in hands | $2 - $10 | $2 - $10 | $2 - $10 | The price could be higher if any specific photo with the documents should be taken |
Each item is subdivided by the type of card being offered. For example, a common credit card with “Fullz” can cost between $8 and $70. Fullz means that for the posted price the buyer is also given additional information on the victim. This can include name, address, Social Security number, driver’s license, and bank account credentials, all wrapped up in one package and all of which enables the buyer to better utilize the stolen credential.
Trustwave SpiderLabs found three “classes” of credit card for sale. Cloned cards with fullz, common credit card with fullz and different classes of credit cards, such as gold, platinum, business, etc.
Cloned cards range in price from $50 to $1,500 with the cost depending upon the credit limit assigned to the card. The higher the limit, the pricier the card. Common cards, as previously noted, run from $8 and $70, per card and generally comes with fullz. The price for the final type varies slightly between regions, $30 to $140 in the U.S. and slightly less in the EU and Asia.
|
Hi guys! Call me Redseller94 Update 2022 LIST CREDIT CARD AND GIFT CARD ***** CREDIT CARD USA (Best Seller) UNITED KINGDOM (Best Seller) AUSTRALIA CANADA FRANCE GERMANY CHILE TAIWAN SPAIN JAPAN ITALY BRAZIL ***** GIFT CARD AMAZON (Best Seller) ITUNES (Best Seller) BESTBUY STARBUCK EBAY XBOX (Best Seller) WALMART TARGET ***** DEAD FULLZ INFORMATION US/UK FULLZ RANDOM BANK US/UK FULLZ WITH ALL BANK (CHASE, HSBC, BARCLAYS, etc…) VALID PASSPORT – DRIVER'S LICENSE – NATIONAL INSURANCE NUMBER – SSN – DOB UPDATED NEW YORK, COLORADO, CALIFORNIA, TEXAS, RHODE ISLAND, ILLINOIS (DRIVER'S LICENSE, SSN, DOB) ***** DUMPS WITH PIN + CLONE CARD |
Selling Fraudulent Supporting Documentation
One class of documentation for sale in these marketplaces shows how much thought criminal actors will go to make their stolen data valuable.
Some sites will create false documentation to help a buyer prove to a bank or financial institution that they are in fact the true owner of the credentials they purchased.

The advertisements for these credit cards are brazen and full of details.
The common verification flow has the person who bought the stolen bank needing to confirm identity to the bank. So, the actor, to prove his identity, must provide a photo with himself holding an ID, like a passport or driver’s license, along with the bank account information.
To provide such picture for verification, malicious attackers utilize the services of Drawer/Artist who can be found on a Dark Web market. The Dark Web artist creates the required ID using the photo a drop person. The drop person – is someone who will physically go to the bank to get the money or use the document as proof for an online withdrawal.

While this form of identification is not the norm in many countries, it can work at a bank with low security standards.



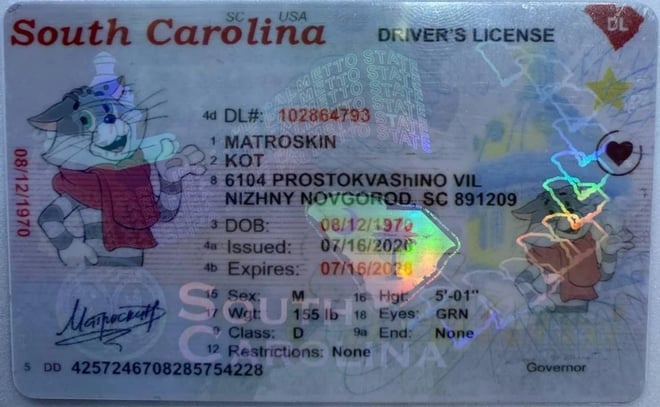
This artist group developed used high-end tools to create a quality finished product. The artists can even add the required holograms and mimick watermarks on the identification documents.

Fake documents. With this approach, even modern verification video calls could be easily passed by introducing such printed IDs.
Bank Accounts
Bank account pricing, $100 to $3,000 per account, is directly tied to the amount of money that can be accessed. The higher the amount that can be stolen, the more expensive the purchase. Additionally, the price correlates to how easy it is to access the bank account as some banks might not be easier for a criminal to fool.
The seller usually mentions the balance on that account along with the victim’s physical address. This can be done to hint at the target’s potential level of wealth, a toney address in Los Angeles or New York City might garner more interest from a buyer.
Typically, those buying a bank account gain online access, the account and routing number, any debit card and PIN information available, the owner’s name and signature, phone number and billing address. The owner’s IP address along with the operating system used to access the account might also be included.
While this information is generally used to digitally access an account, the criminal could go to the financial institution and use this information to simply withdraw the money in person. Stealing the money in this manner is one way to defeat any multifactor authentication that might protect the account, but it also opens up the possibility of the individual being caught and arrested.
Buying Virtual Private Network Credentials
VPN access credentials were the most expensive records SpiderLabs found being advertised. This is logical considering what a threat actor can do once inside an organization. Everything from stealing money, corporate espionage, IP theft, seeding malware and planting ransomware are all on the table once access is gained.
Our researchers found one ad asking $5,000 for access to a corporate network, while another was priced at $2,500 for VPN credentials purportedly to a Korean company with an estimated $7 billion in revenue.
Ads for VPN access can offer a great deal of detail to help persuade a buyer. Sometimes they mention the businesses industry but the price for the access is generally determined by the company’s revenue, as can be seen in this list of examples from the XSS forum. Note that the word ‘jealousy’ in the document is a bad translation for ‘revenue.’
|
“Financial business, Taiwan. 627m of revenue. Palo Alto. 1500$ Big business headquarters, manufacturing, finance, south korea. 7 billion jealous. Pulse. 2500$ Working with insurance, Argentina. 171m revenue. Palo Alto. 500$ Credit business, Indonesia. 99m of revenue. There is a stock symbol. Fortinet. 300$ Headquarters, commodity business, dubai. 25m rope. Palo Alto. 400$ Produce feed for livestock, leaders, myanmar. 227m revenue. Palo Alto. 900$ Univer, UK. 274m jealous. Palo Alto. 300$ Univer, Canada. 645m jealous. Cisco. 600$ Univer, Australia. 635m of revenue. Palo Alto. 600$ Business school, Denmark. 31m revenue. Palo Alto. 200$ Yusa above 20m is relevant. There is Canada, bis on 20m. It's ok too. They are $200 each.” |
VPN access advertisements.
For this price, the seller provides administrator access to a server on the network. The ability to access other machines on the network depends on local permissions and the way the network is configured in that organization.
If a company has a solid cybersecurity defense in place even this level of access might not be enough to do severe damage. The ability to use that access for malicious purposes will be limited in environments that are fairly restricting, use network segmentation, and check for anomalies etc.

INFOGRAPHIC
How Much Is Your Identity Worth on the Dark Web?
The dark web is the digital equivalent of the black market, and there's no limit to the sensitive, personal information available for purchase in the dark underworld of hackers.
ABOUT TRUSTWAVE
Trustwave, A LevelBlue Company, is a globally recognized cybersecurity leader that reduces cyber risk and fortifies organizations against disruptive and damaging cyber threats. Our comprehensive offensive and defensive cybersecurity portfolio detects what others cannot, responds with greater speed and effectiveness, optimizes client investment, and improves security resilience. Learn more about us.


