Introduction
Threat actors are taking advantage of Microsoft OneNote's ability to embed files and use social engineering techniques, such as phishing emails and lures inside the OneNote document, to get unsuspecting users to download and open malicious files. Once clicked, an attacker can use the embedded code for various malicious purposes, such as stealing data or installing ransomware on victims' systems.
Last December, we discovered a malicious campaign involving a trojanized OneNote document delivering Formbook. The campaign is an example of a shift away from macro-enabled documents after Microsoft tightened security measures for files downloaded from the Internet, making macro-based attacks less effective.
We recently observed a notable spike in emails utilizing malicious OneNote attachments with notorious malware strains also shifting to this delivery mechanism. This multi-part blog series highlights recent campaigns we observed using this technique.
What is OneNote?
OneNote is a note-taking application developed by Microsoft and bundled in its Office application suite. It allows users to take notes, organize information and insert files such as images, documents, and even executables. It is a popular application used by many organizations and individuals.
OneNote files use .ONE as a filename extension. A OneNote document consists of sections, pages, and user-created content. Unlike DOCX and XLSX, OneNote does not support VBA macros.
Infostealer
The first campaign uses a fake product inquiry to lure users into downloading a OneNote attachment. Trustwave’s MailMarshal manages to unpack and extract the contents of that OneNote document making it easy to spot suspicious embedded files.

Figure 1. A fake product inquiry email with attached malicious OneNote document. MailMarshal manages to extract the images, texts and executable embedded in the OneNote notebook making it easy to spot suspicious contents.
The OneNote document purports to be a product inquiry document in PDF format. Once the user clicks the ‘View Document’ button, it loads an embedded executable sporting the right-to-left override (RTLO or RLO) trick making it appear as ‘Orderinvpif.pdf’ to the user and flipping the extension ‘pdf.pif’. In addition, the executable masquerades as an Adobe PDF Reader icon. Like the sample we saw last December, the embedded file abuses the RTLO character (U+202E) to disguise the file name making it appear harmless.
An embedded fake inquiry PDF pops out once the executable is clicked. The fake inquiry tricks the user into thinking that the opened file is a legitimate document, but in the background malicious activities were conducted.

Figure 2. Trojanized OneNote document with one section using PDF viewer as a lure to let targets click on the ‘View Document’ button.
Infection chain

Figure 3. High-level view of the infection routine of the campaign with email as initial access vector.
The threat actor created the with PyInstaller, a library that packages Python programs into standalone executables. Using pyinstxtractor, we extracted the contents of the PyInstaller package - the version of Python used to generate the executable - and the possible entry points of the executable. The sample was packed and created with Python 3.10. We investigated each entry point, and what caught our eye was the script ‘contain.pyc,’ which holds the Python bytecode of the primary payload.

Figure 4. Extraction logs of pyinstxtractor for our PyInstaller-based executable, it identified possible entry points and revealed that the executable was packed with PyInstaller 2.1 with Python version 3.10.
Embedded PowerShell Script
While inspecting the bytecode, we noticed it contains a chain of PowerShell commands. The command starts by comparing the current date with the preset start and end date and ensures it runs within the preset time period. It also checks if it is running in virtual environments, like VirtualBox, VMWare, or Hyper-V. Both techniques are used to detect and evade analysis environments.
Using the Get-WinHomeLocation command, the PowerShell code retrieves the current user’s home location or country, followed by the whoami command to get the current username. The user’s home location and username will then create subfolders in the %APPDATA%/Creds/ directory storing the stolen information.
The code then collects system information using the PowerShell command Get-ComputerInfo and stores the information in a text file. Below is additional information collected from the victim:
- Public IP address through the service http://ifconfig[.]me/ip
- Network adapters using the command ipconfig/all
- Browsing history by traversing the %APPDATA% directory of browsers
- Stored WiFi passwords with the command netsh wlan show profile name="<profile>" key=clear

Figure 5. The PowerShell script initially sets up defense evasion like AV scanning path exclusion and VM checks followed by credential harvesting.
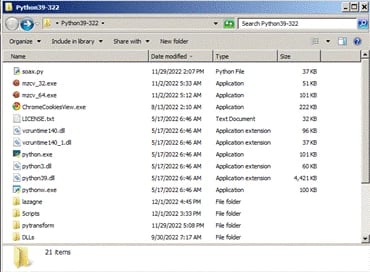
To further collect browser data, the script downloads a ZIP package from https[://]evilextractor.com/wp-content/uploads/2022/12/Python39-322.zip containing a portable Python package and toolsets.

Figure 6. The script downloads a ZIP archive containing a set of tools to assist in harvesting further data.
Included in the package are the utilities ChromeCookiesView and MZCookiesView. These are freeware created by NirSoft that extract cookies, history data, and cache information from web browsers. ChromeCookiesView and MZCookiesView are used by threat actors for malicious purposes.
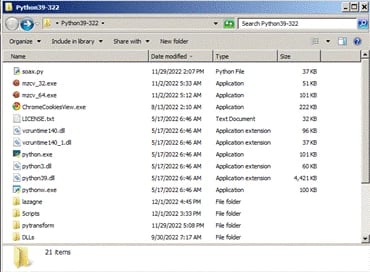
Figure 7. The contents of the ZIP archive include ChromeCookiesView.exe, MozillaCookiesView (mzcv_32.exe, mzcv_64.exe), a python script - soax.py for password harvesting, and all others are part of the Python 3.9 package.
A Python script named soax.py, obfuscated with PyArmor, is part of the toolset used to collect web browser and mail client passwords.

Figure 8. PowerShell Code snippet running the Python script - soax.py, executed against browsers and mail clients to harvest passwords.
Moreover, the PowerShell script searches for images, videos, documents, archives, and text files from victims’ desktops and download folders then copies each file in the %APPDATA%/Creds/ folder.
The stolen data, which ranges from from browser credentials to user files, are stored in %APPDATA%/Creds/ were exfiltrated to a remote FTP server operated by the threat actor. The FTP credentials were embedded in the script.

Figure 9. These are the file extensions of interest being harvested from desktop and download folders of the victims’ machines. All the data stolen is exfiltrated through a remote FTP server controlled by the threat actor. The FTP credentials are hardcoded in the script.
The script downloads another tool called CommandCam directly from the developer’s GitHub repository. The tool captures webcam images from the command line. The images were then stored in the %APPDATA%/Ss/ directory and exfiltrated through FTP on the same server used by the threat actor.

Figure 10. To capture webcam images, it downloads a tool called CommandCam. It also takes a screenshot of the target machine using PowerShell commands.
To cap everything off, the script cleans up all PowerShell logs, downloaded files and captured webcam images to conceal its traces.
Conclusion
Trojanized OneNote documents have grown in popularity among threat actors since we first spotted them in the wild. It is highly likely that threat actors are achieving their objectives using this delivery method in conjunction with tricky social engineering.
This threat is a relevant example of threat actors chaining legitimate open-source and free tools to carry out malicious attacks. These tools tend to be overlooked and could potentially evade security measures. The overall infection chain is simple yet powerful, posing a severe threat to end-users.
In the second part of this series, we’ll go over an infection chain that leads to AsyncRAT malware. We will also provide an overview of other notable malware strains.
Indicators of Compromise
|
ftp[://]191[.]96[.]63[.]60
|
FTP Server
|
|
5a513d230db2bd983575be5902ee2db07dad96c1
|
Orderinvpdf.pif
|
|
2046c77280cb39966b1bbbcab6bdf3d35f5bd72a
|
P0220230123.one
|