When you think about cyberattacks and your business falling victim to one, chances are your mind wanders to a headline-making data breach that exposes legions of personal information about your customers.
It may be easy to overlook another type of attack that can wreak extensive havoc at your organization - and may signal that something even more damaging is underway.
Distributed denial-of-service (DDoS) attacks, which flood your network with unwanted traffic, have become more frequent, powerful and commoditized over the past few years, so much so that the FBI is asking businesses to share details about these incidents so it can better understand how they are being launched and by whom.
You may consider DDoS attacks a mere nuisance, but they can disrupt your organization and grind your productivity and operations to a halt. And they're not going away. Why? Mainly because your adversaries extract too much value from them.
1) It nets them easy money.
Malicious hackers skilled in the art of disabling servers, usually with powerful botnets (which may consist of compromised IoT devices) at their disposal, can bring businesses to their knees - and then demand payment to call off the dogs. Gaming companies and media brands are trendy targets of these extortion-style attacks. Aware that the prospect of downtime is so undesirable for companies, craven crooks have even taken to sending blackmail letters merely threatening an attack, with no plans on actually following through.
2) It gives them a convenient smokescreen.
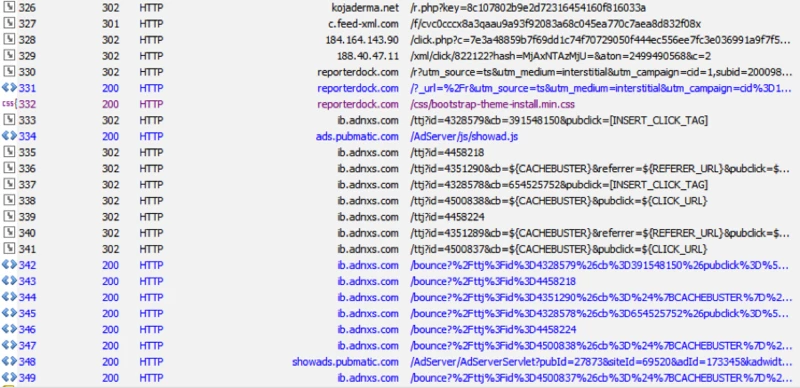
Cybercriminals like to create confusion - and they sometimes turn to DDoS attacks to distract and misdirect resource-deprived organizations from their primary goal: to pillage sensitive data. DDoS attacks are optimal subterfuge because they create noise and chaos that will attract the brunt of attention from your IT staff, leaving wide open the opportunity for your foes to simultaneously infiltrate your network and mask data exfiltration.
3) It can be the digital pretext for a physical attack.
Sometimes a DDoS attack is merely a means to an end. Earlier this week our SpiderLabs team revealed a web-based vulnerability in a popular brand of printers that could result in denial-of-service attacks. Our researchers theorized that attackers could launch the printer attack and show up at the target organization pretending to be the "technician" called to fix the problem. This impersonation could net them direct physical access to IT resources that they might never have been able to access remotely.
How to Defend Against Them
Given the trends, DDoS attacks are clearly difficult to stop. But there are efforts you can take to limit your exposure and minimize the harm they can cause. As always, defense-in-depth strategies that include performance baselining, risk assessments, perimeter protection, patching, vulnerability scanning, threat detection, and incident readiness and response can go a long way toward curbing the intensity and impact of these events.
DDoS mitigation services can also help handle high-volume, intense attacks, known as volumetric attacks. To gain more upstream protection, you can also talk to your internet service provider to ensure they are performing mitigation methods such as protocol filtering.
As an additional resource, Carnegie Mellon University's Software Engineering Institute offered useful suggestions, including the importance of shoring up network architecture by spreading out data centers, building in redundancy and avoiding single points of failure.
To learn how Trustwave can help, see our Managed Detection and Response services page.
Dan Kaplan in manager of online content at Trustwave.