As the world celebrates International Women’s Day, it’s an unfortunate reality that cybersecurity, like many other industries, is often thought of as a male dominated field. Like so many other sectors of society, women sometimes struggle to break through and are still underrepresented in leadership positions. Despite the obstacles, many female cybersecurity professionals are breaking barriers and setting new precedents, serving as examples for the women who will follow in their footsteps.
One of the huge benefits of working as a global team is the benefits, diversity and different perspectives that are applied to solving difficult problems. Trustwave SpiderLabs is fortunate to benefit from this at all different career levels. From Analysts all the way up to Directors, we are proud gender is not a barrier to advance in a highly technical field. Five of our team members, Anna Oliveira, Olga Barinova, Tanya Secker, Eduel Neyra and Therese Mendoza, sat for this interview, so that we could explore their experiences in the cybersecurity industry and learn more about what motivates them. Find the full interview below.
Q: Could you briefly introduce yourself and describe your role here at Trustwave?
Anna: Hello, my name is Anna; I am the Director of Operations for our Global SpiderLabs practice. My primary responsibilities are to manage our customer service, processes, product, and service delivery, enhancing our practice bridge between our internal teams in favor of a delightful experience for our customers.
Tanya: My name is Tanya Secker and I am the Practice Lead for EMEA. I also lead QA and the AppSec Think Tank globally. I have been in penetration testing for over 15 years, specializing in apps for over a decade and I have been at Trustwave SpiderLabs for 13 years.
Olga: My name is Olga Barinova and I'm a Senior Security Consultant at Trustwave SpiderLabs. I've been working here for 2 years now. My main responsibilities are to perform penetration testing against web applications, conduct source code review and communicate with clients helping them to fix issues.
Therese: I'm Therese Mendoza, a Senior Security Consultant at Trustwave SpiderLabs. I’ve been working here for 5 years. I handle most of the Mobile and Web application penetration testing engagements.
Eduel: My name is Mary Eduel Neyra, a Managing Consultant of Trustwave’s SpiderLabs - Vulnerability Management Services. My daily responsibilities include delivery, QA and management. I’ve been in Trustwave for almost 5 years now. Our team does basic penetration testing, but our main responsibility is managed scanning for Network and Web Application, as well as database.
Q: Tell us about your career path and why you chose cybersecurity?
Anna: I have always had a passion for immersing myself in other cultures, serving, and creating things. I thought I would be a chemist or a CIA agent, but after going to school for Hospitality Management in Rio, I set out to see the world. This path is where I fell in love with people! Even more where I decided that anything I did in my career would include the art of understanding people, with a focus on their needs, and coming up with creative ways to serve or make their lives more enjoyable. During this pursuit, I developed a couple of vital skills that would shape my career trajectory across several industries. Five years ago, I decided to venture to do something entirely outside my comfort zone, and here I am, loving it.
Olga: When I studied in Moscow State University, I had no doubt I was going to be a software engineer, because I was in love with coding. But at some point, I found a few friends who could do some mysterious things on their laptops and I wasn't completely unaware how they did it, so I started to look into it. It was hacking (mostly CTF)! When there is something that I don't know I always tend to delve into it. So, cybersecurity drew me in.
Tanya: I have always had a curious and somewhat logical mindset and this lent itself well to cybersecurity.
Eduel: This was not included in my plan. I just applied to a company that was looking for fresh graduates and got a job, then I was surprised what I got myself into. I just learned about this field when I started working, and who would have thought that I would love this. I find cybersecurity very interesting, fun and relevant. It is an ever growing field. I take pride in what we do and how we help/impact the world.
Therese: At a young age, I was fascinated with computers. I continued to take this path into university until I graduated with a bachelor’s degree in Information Technology. I started as a Java programmer, but opportunity knocked when there was a job offered for penetration testing. This really caught my attention and I decided to pursue this field. For me, it is a rewarding job. It's fun when you start digging into the application and you can find one vulnerability after another. It's gratifying to know you're helping protect people's privacy and security. It can also be a mentally engaging and exciting field.
Q: Were there any obstacles you felt you had to overcome in your career path?
Olga: This work requires creativity on a day-to-day basis. Sometimes when you have bad days, you just don't have the inspiration to produce creativity. In such moments I think about why I didn't choose the "software engineering" path in my career – which is more about solving a clearly defined problem. I would just need to solve it rather than improvise trying to find a way how to hack a system. Luckily, I don't have many of those days, so I certainly enjoy my work.
Therese: Absolutely. There's a handful of research work that needs to be done, especially with evolving technology. Then, having to test over and over again making sure you're doing it correctly or not overlooking any vulnerabilities. It can be a work that demands detailed attention, effort, and patience. Clients are another big part of the job. Some are genuinely interested in their security posture and others not so much. So as a consultant, you have to be firm with your findings and don't doubt yourself.
Anna: There have always been obstacles in my life. From the moment I left my home country with my family as a young girl -- I lived in three different countries by the time I was twenty-three. I have had to adapt very quickly to learning new languages to communicate. Today, one of the worst struggles in my career is not delivering the way I want for every client. I eventually realized that many of the obstacles in my life were based on external factors, and even though they impact me, I decided it’s better to treat them as learning experiences. This belief allows me to focus on making the most of every situation and seeing the positive in anything, which has immensely helped me easily overcome many difficulties.
Q: What advice would you have for other women who want to work in cybersecurity?
Olga: Nothing is impossible. It's not as difficult as it sounds. Just take it one step at a time.
Therese: Challenge yourself. Don't fear a field that may seem intimidating. It's perpetual learning and if you're passionate about cybersecurity and technology, then do it. It's definitely a male-dominated industry, but once you get to where you want to go, it can be very fulfilling. Keep in mind that every small step counts and the insight of every person, women including, makes a huge impact.
Tanya: Compromise boxes/apps/networks but never yourself. A good sense of who you are will help you achieve greatness in the industry.
Eduel: If others can do it, you can do it. Trust yourself! Know your strengths and weaknesses and work on it. Don’t be intimidated and overwhelmed, take one day at a time.
Anna: Things are always changing fast, especially in this industry. If you are aware, at peace with what is important to you, and willing to put the work in, you will succeed. Because with a lot of hard work, trust in yourself, and a “keep going” mentality, you can make your path to creating, changing, and discovering some amazing things that will make an impact -- albeit not always “perfect,” but that’s not the goal. Never underestimate your judgments, ideas, or inventions, and don’t forget to have fun along the way!
Q: What's your favorite career accomplishment? Any notable findings or discoveries?
Olga: In my modest career I wrote a couple of blogposts about interesting vulnerabilities I found ("HQL Injection Exploitation in MySQL", "Jolokia Vulnerabilities - RCE & XSS"), got a few CVEs (CVE-2019-11628, CVE-2018-1000129, CVE-2018-1000130, CVE-2017-12629) and obtained OSCP and OSWE certifications.
Therese: I have lot of favorites, but I’m very much interested in finding IDOR (Insecure Direct Object References) vulnerabilities. One instance is where I bypassed the OTP verification process of an application by manipulating the response from the server that led to a complete account takeover.
Tanya: Holding various CVEs, building up the appsec practice in EMEA for Trustwave SpiderLabs, being chosen as a Woman to Watch by SC Magazine in 2018.
Eduel: I was very happy when I first compromised a domain, I will forever remember that moment. I was very delighted whenever we won a deal, renewed a contract and gave the client the best service they deserve. I am most accomplished when I was able to help our organization improve its processes, services, and delivery thus helping more people understand not just our clients, but the importance of cybersecurity.
Anna: I am not a “hacker,” but I have had a few memorable accomplishments:
- Being apart of the G-20 summit logistics and event committee at the age of nineteen and creating an efficient logistics plan to support the many political delegates from across the globe.
- Developing and triumphantly delivering the FCO – World Cup 2014 delegate logistics and security plan, where I created a process resulting in a 35% increase in business retention -- all through customer service.
- Most recently, in Trustwave, I created a manual campaign that resulted in wide revenue recognition of 3.4 Million dollars in just over nine months.
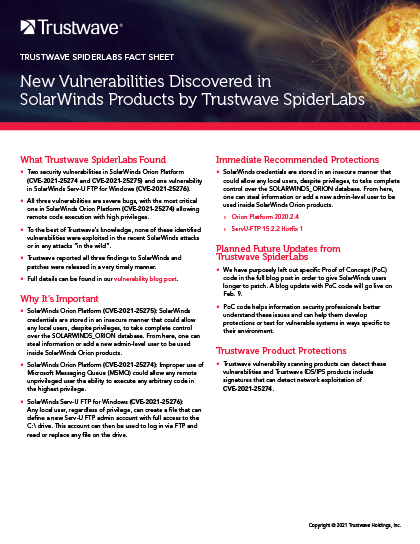
FACT SHEET
New Vulnerabilities Discovered in SolarWinds Products by Trustwave SpiderLabs
Download our fact sheet on the SolarWinds vulnerabilities that Trustwave SpiderLabs has discovered. All three vulnerabilities are severe with the most critical one allowing remote code execution with high privileges.