This is the second installment in Trustwave’s in-depth tour of our Security Colony platform. For a broad overview of what Security Colony offers please read 5 Ways CISOs Can Leverage the Power of Trustwave Security Colony.
Self-evaluation in any area, much less cybersecurity, can be challenging. Is my performance at work strong and consistent? Am I being friendly to my neighbors? And as Billy Joel so wisely pointed out, sometimes an outside opinion is needed because "Can't you tell that your tie's too wide?"
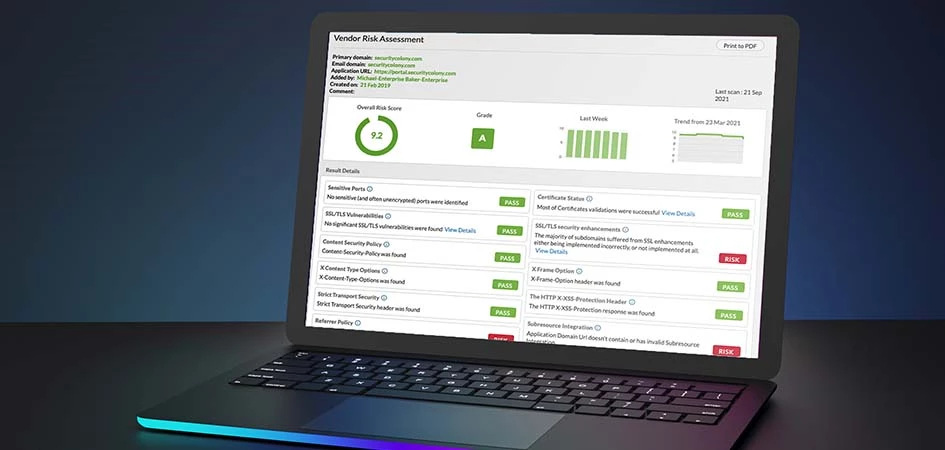
To remedy this situation on the cybersecurity, if not fashion, front Trustwave Security Colony features a Vendor Risk Assessment tool that allows an organization to hold a mirror up to its online self so it can see how its online presence appears to others, especially threat actors.
Trustwave offers several levels of service with the Vendor Risk Assessment tool. The first is free, like a great deal of content provided by Security Colony. It allows an organization to run a scan on its domains.
The second level is for Security Colony subscribers. It has the added functionality of scanning a preset number of the client's vendors' domains and allows for additional vendor slots to be purchased. There are three packages available. Startup provides for the registered domain (so one) to be checked. Core starts with 10 domains, and with Enterprise, this is bumped up to 100 domains. If needed, additional slots are available for purchase.
How the Vendor Assessment Tool Works
Scanning is, in fact, a bit of a colloquialism; Security Colony does not really "scan" anything. Instead, what happens is we monitor and report on publicly available information that is published by a client through their website and from its third parties.
To do this, we use a variety of sources such as Breachsense, Pastebin, GHOSTBIN, Shodan, server fingerprinting using JARM, plus other tests that we have developed ourselves to collect information published on the website we are reviewing.
This process entails assessing security misconfigurations and vulnerabilities related to server configuration, including:
- Whether an organization has a strong process for correctly configuring all their encryption (SSL/TLS) certificates
- Whether an organization has insecure (ie. unencrypted) ports open to the Internet
- DNS server configuration.
There is also an email component with our tool checking for security misconfigurations and vulnerabilities related to email system configuration, including:
- Whether an organization uses strong email security technology (SPF and DMARC)
- Whether employees of an organization have used their corporate email addresses on external accounts, and whether they have then been the subject of a data breach.
The last aspect has us evaluating security misconfigurations and vulnerabilities related to critical web applications.
Unlike other security checks such as pen-testing, Security Colony Vendor Assessment does not require access to an organization's system. Instead, we can gather all we need from publicly available sources.
The Vendor Assessment Process
Trustwave realizes that this is a self-assessment tool, so we built the feature to make it as simple as possible for even a novice to get started. Essentially, when entering a domain to review, you enter the primary domain, an email domain, if different, and an application domain.

Entering a domain simply requires filling in these two slots.
Once the tool completes its assessment a report is generated along with a corresponding list of recommendations.

A generic example of a typical report generated using the Vendor Assessment tool.
For example, the tool conducts a check for sensitive ports. This check determines whether your Primary Domain exposes any potentially sensitive services such as administrative interfaces or database endpoints. If a problem is found, it is highlighted in the report with the following recommendation:
“If this check is marked as ‘RISK’ and this is your domain, we recommend that you review whether there is need to expose these interfaces to the Internet and shut them down where possible.”
The Vendor Assessment tools uses the same process for all the assessed areas, such as certificate status, SSL/TLS Vulnerabilities, etc.
If the recommended actions are beyond the user’s ability, Trustwave can step in and help. A client can make the request via email and Trustwave will respond within 24 hours.
Once the client creates an assessment in the system, it generates a monthly report and sends it to the client.
The Security Colony Vendor Assessment Credo
Security Colony is built on the concept that the best tools to share with others are those that are trusted, battle-tested, and ready to be used rather than starting from scratch each time. This thought process not only enables those in need of a cybersecurity consult or help obtain that information quickly and in a cost-effective manner.